Bridging the Git-to-Jira Gap: How Generative AI Finally Unifies Your Engineering Data
Stop manually matching GitHub PRs to Jira tickets in Excel. See how Keypup's AI Agent instantly translates business goals into technical execution metrics.
Learn about SOC 2 compliance and how software companies can achieve it efficiently. Discover tools that can facilitate secure coding practices, change management, vulnerability management, and more.

SOC 2 (System and Organization Controls 2) compliance is a standard developed by the American Institute of CPAs (AICPA) that helps organizations ensure the security, availability, processing integrity, confidentiality, and privacy of their customers' data.
Compliance with SOC 2 is based on five trust principles: security, availability, processing integrity, confidentiality, and privacy. To be SOC 2 compliant, an organization must demonstrate that it has adequate controls and processes in place to ensure that these principles are met.
The SOC 2 audit is conducted by a third-party auditor who examines the controls and processes that an organization has in place to meet the trust principles. The auditor then issues a report that outlines the organization's level of compliance with the SOC 2 standard.
SOC 2 compliance is particularly relevant to technology companies that provide services to other organizations, such as cloud computing providers or software as a service (SaaS) companies. However, any organization that collects or processes customer data can benefit from SOC 2 compliance.
Some of the SOC 2 prerequisites that are related to the software development lifecycle (SDLC) include:

These are just a few examples of the SOC 2 prerequisites that are relevant to the software development lifecycle. The specific prerequisites that an organization must meet will depend on its unique situation and the nature of its business operations.
Achieving SOC 2 compliance can be a daunting task if you are not armed with the right tools and processes to facilitate the audit as early as possible in your software development processes. Here, we’ve compiled a list of tools aimed at facilitating each of the prerequisites mentioned earlier.
Code analytics tools such as SonarQube or Snyk can play a vital role in facilitating secure coding practices, which is one of the requirements for SOC 2 compliance. By automating the process of identifying vulnerabilities in your code, these tools help minimize the risk of security breaches, optimize coding practices, and ultimately shorten the time required for code reviews.
With SonarQube, for example, you can analyze your codebase for vulnerabilities, bugs, and code smells in real time. The tool provides detailed reports and metrics, including a code coverage report, which can help you identify areas of your codebase that require additional testing. Furthermore, SonarQube integrates with the most popular development environments and source code management tools, allowing you to automate code analysis and review as part of your development workflow.
Snyk is another powerful code analytics tool that helps identify vulnerabilities in your codebase by scanning your code and open-source dependencies for potential security flaws. Snyk can also integrate with your development environment and provide continuous monitoring, making it easier to identify and remediate vulnerabilities as they arise.
By implementing these tools as part of your software development process, you can minimize the risk of security breaches, improve the overall quality of your codebase, and meet the secure coding practices requirement for SOC 2 compliance.
By using Keypup's Audit and Compliance Dashboard to automate compliance tracking and reporting, software companies can save significant time and effort in the SOC 2 compliance process. Some specific time-saving benefits include:
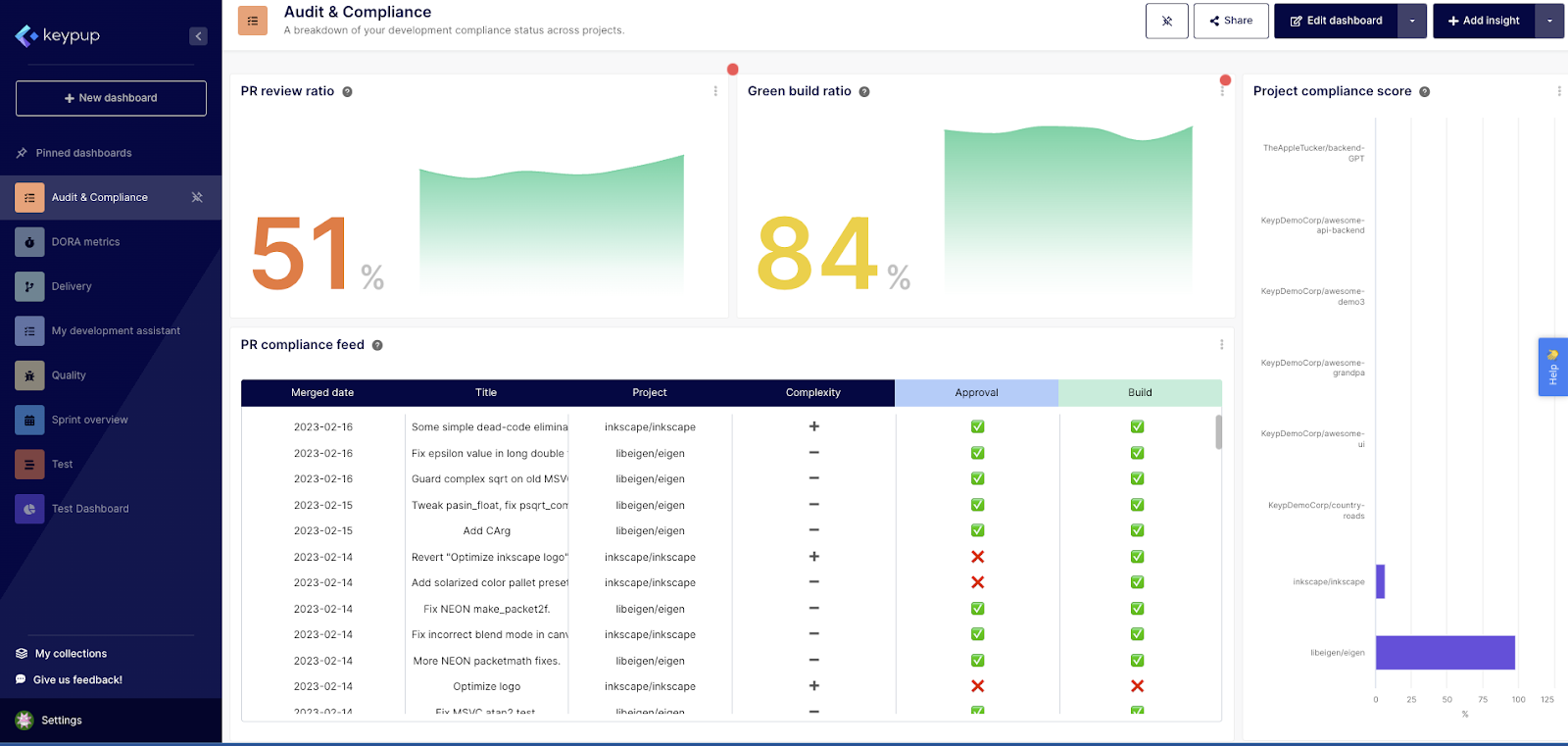
In summary, by using Keypup's Audit and Compliance Dashboard to automate compliance tracking, software companies can save valuable time and resources, streamline compliance workflows, and ultimately achieve SOC 2 compliance more efficiently.
Vulnerability management tools such as Trivy or Detectify can significantly help software companies achieve SOC 2 compliance by providing an automated and efficient way of identifying and addressing vulnerabilities. Here are some ways these tools can assist with SOC 2 compliance:
By using vulnerability management tools, software companies can save significant time and effort in identifying and addressing potential vulnerabilities, thereby helping them achieve SOC 2 compliance more efficiently.
ForgeRock, Okta, GCP IAM, AWS IAM, or Azure IAM are identity and access management (IAM) solutions that help simplify the process of managing access control, which is a critical component of SOC 2 compliance. By using these tools, organizations can set up centralized authentication and authorization processes, manage user identities, and monitor user access to resources. These tools also provide features such as multi-factor authentication (MFA), single sign-on (SSO), and password management, which can help organizations comply with access control requirements under SOC 2.
However, for early-stage startups or organizations with limited resources, implementing such IAM solutions can be challenging due to the high costs and complex setup process. In such cases, here are some of the steps to access control management:
By following these steps, organizations can establish and maintain effective access controls, which is a key component of SOC 2 compliance, without the need for IAM solutions.
Data protection solutions such as Zscaler, Palo Alto or GCP Data Loss Prevention are designed to provide robust data security and help organizations adhere to strict data protection regulations like SOC 2. These tools help ensure data security in several ways:
By implementing data protection solutions, organizations can strengthen their data security posture, meet regulatory requirements, and achieve SOC 2 compliance.
SOC 2 compliance can often seem like a daunting and stressful task, but with the right tools and processes, it doesn't have to be. By following a step-by-step guide and implementing automated solutions, achieving SOC 2 compliance can be much easier and less stressful than you might expect.
One of the key benefits of automating SOC 2 compliance requirements is that it can significantly reduce the time and effort required to prepare for an audit. By implementing tools such as SonarQube, Snyk, Keypup's Audit and Compliance Dashboard, and Trivy, organizations can streamline their compliance workflows, automate compliance tracking and reporting, and identify vulnerabilities in their codebase more efficiently.
Moreover, automating SOC 2 compliance can also help in improving the overall quality of an organization's software development process while minimizing the risk of security breaches and enhancing the overall quality of their codebase, which can lead to better performance, fewer bugs, and a more positive user experience.
While achieving SOC 2 compliance is undoubtedly an important goal for any organization that collects or processes customer data, it doesn't have to be a stressful or overwhelming experience. By following this guide and implementing the right tools and processes, organizations can achieve SOC 2 compliance more efficiently and effectively than ever before. So don't be intimidated by the SOC 2 compliance process — with the right approach, you can achieve compliance with confidence. Start with Keypup’s Audit and Compliance Dashboard today!
Join teams already using AI to make data-driven decisions faster than ever.

Stop manually matching GitHub PRs to Jira tickets in Excel. See how Keypup's AI Agent instantly translates business goals into technical execution metrics.

Developers hate engineering metrics because they feel like surveillance. Learn how to use Keypup's AI to shift the focus from individual micromanagement to systemic SDLC improvement.

Discover why internal DIY dashboards and basic LLM wrappers just create 'noise.' Learn how Keypup’s NLP platform goes beyond plotting metrics to actively diagnose your SDLC bottlenecks and prescribe actionable improvements.